copyright is a hassle-free and reliable platform for copyright buying and selling. The application features an intuitive interface, large buy execution velocity, and useful industry Examination applications. It also offers leveraged trading and different buy styles.
Some cryptocurrencies share a blockchain, while other cryptocurrencies work by themselves individual blockchains.
More safety steps from either Risk-free Wallet or copyright would have diminished the chance of this incident developing. As an example, utilizing pre-signing simulations would have permitted employees to preview the spot of the transaction. Enacting delays for large withdrawals also might have given copyright time for you to evaluate the transaction and freeze the funds.
Many argue that regulation efficient for securing banking institutions is significantly less successful while in the copyright Room a result of the sector?�s decentralized character. copyright demands far more protection restrictions, but In addition it requires new methods that take into account its differences from fiat financial establishments.
If you want aid acquiring the page to begin your verification on cell, faucet the profile icon in the very best suitable corner of read more your home webpage, then from profile pick out Id Verification.
This tactic seeks to overwhelm compliance analysts, regulation enforcement, and blockchain analysts by doing A large number of transactions, both by DEXs and wallet-to-wallet transfers. Following the pricey endeavours to hide the transaction trail, the final word aim of this process might be to convert the resources into fiat forex, or currency issued by a govt such as the US dollar or perhaps the euro.
These risk actors were being then capable of steal AWS session tokens, the temporary keys that enable you to request short term qualifications in your employer?�s AWS account. By hijacking Lively tokens, the attackers had been ready to bypass MFA controls and acquire use of Safe Wallet ?�s AWS account. By timing their initiatives to coincide with the developer?�s typical do the job hours, Additionally they remained undetected until the actual heist.}
 Daniel Stern Then & Now!
Daniel Stern Then & Now!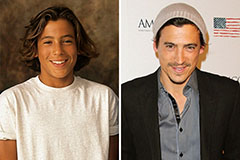 Andrew Keegan Then & Now!
Andrew Keegan Then & Now! Rachael Leigh Cook Then & Now!
Rachael Leigh Cook Then & Now! Andrew McCarthy Then & Now!
Andrew McCarthy Then & Now! Sarah Michelle Gellar Then & Now!
Sarah Michelle Gellar Then & Now!